Email Tech 2004

In the last few weeks I’ve upgraded my email environment here and there, and I thought it would be worth passing on hints in the areas of mail-sending service and security.
I’m sure that quite a few of my readers, who are a pretty bleeding-edge bunch, know about all this stuff and mastered it years back. Typically I’m sort of at the trailing edge of the leading wave of early adopters; so I’ll bet that there are a few folks out there for whom this will be useful.
Getting Your Mail Sent · If you travel a lot, there’ve probably been times when you wrote an email, hit “Send”, and Things Went Wrong. Whether you understand how the email machinery works or not, the basics are easy: your email client doesn’t actually know how to get mail to its destination, it has to hand off to something called an “SMTP Server” to do the heavy lifting. If you’re in the same environments all the time, for example your office and your home, this got set up for you when you were just getting going and you’ve never really noticed it happening. But when you get out on the road, sometimes things don’t work so smoothly.
Bad Options ·
There are a few things you can do. If you know what ssh is,
and you have an ssh link back to your job, you can do “Port
Forwarding” and use the server there. Of course, you have to have
ssh and be willing to figure this out. Blecch.
Alternatively, you can run an SMTP server right there on your own machine. Mac OS X has this semi-built-in, and I’m sure that there are ways to do it on Windows too. Mind you, you’ll quickly discover that there’s a reason that mail servers are normally well-configured always-on computers in a back room somewhere. Setting this up and managing it is typically more work than you’d like to do. Blecch Blecch.
Or, when you’re at a hotel or a conference or a train station and you can’t send mail, you can try finding tech support and explaining the problem. Blecch Blecch Blecch.
Mailhop To the Rescue ·
It turns out there’s a good answer, and it’s provided by
DynDNS.org, about whom I’ve written
before. It’s called
MailHop, and it’s
basically this big SMTP server out there in the Internet somewhere.
You sign up with them and pay them $14.95/year, and in return they give you a
login and password with which you can send up
to 150 messages per day.
You have to go to your email settings and type in
outbound.mailhop.org and your login and password, and from that
moment on, sending mail Just Works, wherever you are.
Now here’s something clever; when I’m sitting here in my home office and I send mail, it takes about twenty seconds to connect to the the MailHop server; at first I thought they were just busy, but now I realise that this is a simple but effective anti-spam measure. If it takes thirty seconds to send a message, you just can’t spam. At my most manic, I can’t cook up emails faster than one or two per minute, so it’s just not a problem.
Once you think of it, the idea of farming out your email sending to a professional email sender is a no-brainer; why on earth should companies and individuals have to deal with the Internet Wilderness when we can pay pros to do it, and to do it for peanuts. Also, this fits neatly into the spam solution that Cutting, Sifry, Zawodny and I cooked up at the Foo camp; if it already makes sense for email transmission to go through specialist email transmitters as a (very cheap) paid service, why not put the spambusting tech right there?
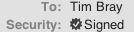
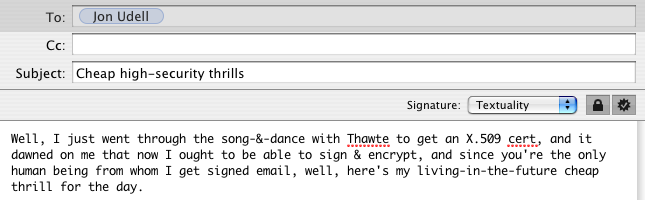
Security, Signing, Crypto, Etc. · From time to time, I see a little tick-mark on incoming email (pictured right) that means it’s been digitally signed. I thought that the way the world’s going, this couldn’t possibly be a bad idea and I should too. Well, the OS X Mail program tells you, if you have a Mail Signing Certificate, how to import and use it. So, how do you get such a certificate? Google, believe it or not, was no help. Eventually I figured it out. Below is a screen-shot from a mail composition window where I’m writing an email to Jon Udell, I picked him because he’s one of the people I get signed email from. Not only did I sign this but I encrypted it too, since I have Jon’s public key as a side-effect of his signing things. So in this case, Jon has a great deal of certainty that this is coming from someone with my email address, and I have great certainty that nobody but Jon can read the message. Of course, the picture below defeats the effect of all the advanced mathematics and public-key infrastructure, oh well.
Anyhow, here’s a step-by-step walk-through. Some parts are Mac-specific, but I think this might still be useful.
Go to the Apple Knowledge base and read the helpful little tutorial there.
Thawte and Verisign are the first two names that come up when you go looking for certificate providers. I went to Thawte because a lot of people I respect hate Verisign; but then Christopher Elkins told me that Verisign now owns Thawte, so if you can get a cert (the in-crowd all say “cert” not “certificate”) from a non-Verisign source, I wouldn’t know now. Neither of these guys make it easy to find the service where they’ll give you a free certificate for signing email, because they really want to sell industrial-scale security services to business. Fair enough, but you can find what you need here.
By the way, Mr. Elkins also pointed me to this excellent tutorial on how to get certificates going on Mac OS X.
Getting the certificate is a multi-step process, but fairly pain-free. Unfortunately, they want to integrate tightly with the browser and some browsers aren’t quite hip yet; I had to go in with Mozilla, let Thawte stuff the certificate into Mozilla, then get Mozilla to back up the certificate to a disk file.
Once you get your certificate stored in a .p12 file, then
you double-click on it and all that highly-polished Mac automation just takes
over and you’re home free.
Of course, another approach would be to go with PGP, which I understand is much more hip, funky, and fashionable, in particular among the heavy geeks. But this seems to make my email more secure than it would be without it.
And, by the way, there’s no reason that my email has to be signed by my own email client; I bet you could set up something like MailHop to sign stuff on the way through (at a very small charage of course) and hey, we’re back to that death-to-spam infrastructure. Sounds inevitable to me.
The Cost ·
There’s no free lunch. Here’s the full raw source of a signed (not
encrypted)
email from myself to myself, where the message is the single word “Boo!”.
Including that and From, To, Date, and
Subject, I count 133 bytes of payload; the whole message
is 4,895 bytes in length; which is to say 2.7% payload, 97.3% overhead.
Still, on balance I think we do make progress.
From XXXXX@XXXXXXXXXXXXXX Thu Jan 22 17:34:32 2004
Return-Path: <XXXXX@XXXXXXXXXXXXXX>
Received: from intergate.uniserve.ca ([unix socket])
by intergate.uniserve.ca (Cyrus v2.1.11-SDF) with LMTP; Thu, 22 Jan 2004 17:31:06 -0800
X-Sieve: CMU Sieve 2.2
Received: from mx1.uniserve.ca ([216.113.192.42])
by intergate.uniserve.ca with esmtp (Exim 4.05)
id 1AjqA6-0000BJ-00
for XXXXX@XXXXXXXXXXXX; Thu, 22 Jan 2004 17:31:06 -0800
Received: from outbound.mailhop.org ([63.208.196.171])
by mx1.uniserve.ca with esmtp (Exim 4.22)
id 1AjqA5-0008pW-0p
for XXXXX@XXXXXXXXXXXXXX; Thu, 22 Jan 2004 17:31:05 -0800
Received: from XXXXXXXXXXXXXXX.uniserve.ca ([XXX.XXX.XXX.XXX] helo=[192.168.1.100])
by outbound.mailhop.org with asmtp (TLSv1:RC4-SHA:128)
(Exim 4.20)
id 1AjqA4-000Fhh-5x
for XXXXX@XXXXXXXXXXXXXX; Thu, 22 Jan 2004 20:31:04 -0500
Mime-Version: 1.0 (Apple Message framework v609)
To: Tim Bray <XXXXX@XXXXXXXXXXXXXX>
Message-Id: <BB681B36-4D43-11D8-B206-000A95A51C9E@XXXXXXXXXXXXXX>
Content-Type: multipart/signed; micalg=sha1; boundary=Apple-Mail-4--122533140; protocol="application/pkcs7-signature"
From: Tim Bray <XXXXX@XXXXXXXXXXXXXX>
Subject: Signed
Date: Thu, 22 Jan 2004 17:30:30 -0800
X-Mailer: Apple Mail (2.609)
X-Mail-Handler: MailHop Outbound by DynDNS.org
X-Report-Abuse-To: abuse@dyndns.org
X-MHO-User: XXXXXXXXXXXX
X-Scanner: OK. Scanned.
--Apple-Mail-4--122533140
Content-Transfer-Encoding: 7bit
Content-Type: text/plain;
charset=US-ASCII;
format=flowed
Boo!
--Apple-Mail-4--122533140
Content-Transfer-Encoding: base64
Content-Type: application/pkcs7-signature;
name=smime.p7s
Content-Disposition: attachment;
filename=smime.p7s
MIAGCSqGSIb3DQEHAqCAMIACAQExCzAJBgUrDgMCGgUAMIAGCSqGSIb3DQEHAQAAoIIGHDCCAtUw
ggI+oAMCAQICAwuKuTANBgkqhkiG9w0BAQQFADBiMQswCQYDVQQGEwJaQTElMCMGA1UEChMcVGhh
d3RlIENvbnN1bHRpbmcgKFB0eSkgTHRkLjEsMCoGA1UEAxMjVGhhd3RlIFBlcnNvbmFsIEZyZWVt
YWlsIElzc3VpbmcgQ0EwHhcNMDQwMTIyMjMzOTA2WhcNMDUwMTIxMjMzOTA2WjBGMR8wHQYDVQQD
ExZUaGF3dGUgRnJlZW1haWwgTWVtYmVyMSMwIQYJKoZIhvcNAQkBFhR0YnJheUB0ZXh0dWFsaXR5
LmNvbTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAMYiIlrf7yTblabXBlwkonodVyp+
W7Oo8w71ErSW7mKramEBAkfkUnPmbRqcS2wqFaK34GbQMk/1vcOxo2AmfmFVec13SWKi0YzXC8xf
9SbjfQU1tXiC9LJB1HeOO46UVRqTNeayruz2pQBztvYF76G5sGmwKjoR/DhimwUM579MaJln38SK
UQ6Ya768DwyaDNY7yDWYh1gUxizx71QkzyRCPQdmq6g1ebrVYyoBE33BXQRNGZm2zrlI5JBQ4oax
E0Cz3BjR8iZFzK/AhFGDllZYuojf7iZuaNhWr3aWAvHNyLHVMaxXNFb/CUri5c7StFVEgXUVvlgP
eSHIPg9gqaECAwEAAaMxMC8wHwYDVR0RBBgwFoEUdGJyYXlAdGV4dHVhbGl0eS5jb20wDAYDVR0T
AQH/BAIwADANBgkqhkiG9w0BAQQFAAOBgQBQAlJ/qQJmtQN966ahSWiovhjWj5Qwk6BnPP+Fjfbo
9guSIWWBw2DEXh8nPT4WJchZSVz4SwDtZ0SZ2PWWToRo/Dmpv+ehzNNhR/y2CdU/zNo+kSShBhc6
HNtp6A0+Yh6Vw0Y+qHa0EKppOJM2D5WTExycYjHU8Xs+dLktAmKqlzCCAz8wggKooAMCAQICAQ0w
DQYJKoZIhvcNAQEFBQAwgdExCzAJBgNVBAYTAlpBMRUwEwYDVQQIEwxXZXN0ZXJuIENhcGUxEjAQ
BgNVBAcTCUNhcGUgVG93bjEaMBgGA1UEChMRVGhhd3RlIENvbnN1bHRpbmcxKDAmBgNVBAsTH0Nl
cnRpZmljYXRpb24gU2VydmljZXMgRGl2aXNpb24xJDAiBgNVBAMTG1RoYXd0ZSBQZXJzb25hbCBG
cmVlbWFpbCBDQTErMCkGCSqGSIb3DQEJARYccGVyc29uYWwtZnJlZW1haWxAdGhhd3RlLmNvbTAe
Fw0wMzA3MTcwMDAwMDBaFw0xMzA3MTYyMzU5NTlaMGIxCzAJBgNVBAYTAlpBMSUwIwYDVQQKExxU
aGF3dGUgQ29uc3VsdGluZyAoUHR5KSBMdGQuMSwwKgYDVQQDEyNUaGF3dGUgUGVyc29uYWwgRnJl
ZW1haWwgSXNzdWluZyBDQTCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEAxKY8VXNV+065ypla
HmjAdQRwnd/p/6Me7L3N9VvyGna9fww6YfK/Uc4B1OVQCjDXAmNaLIkVcI7dyfArhVqqP3FWy688
Cwfn8R+RNiQqE88r1fOCdz0Dviv+uxg+B79AgAJk16emu59l0cUqVIUPSAR/p7bRPGEEQB5kGXJg
t/sCAwEAAaOBlDCBkTASBgNVHRMBAf8ECDAGAQH/AgEAMEMGA1UdHwQ8MDowOKA2oDSGMmh0dHA6
Ly9jcmwudGhhd3RlLmNvbS9UaGF3dGVQZXJzb25hbEZyZWVtYWlsQ0EuY3JsMAsGA1UdDwQEAwIB
BjApBgNVHREEIjAgpB4wHDEaMBgGA1UEAxMRUHJpdmF0ZUxhYmVsMi0xMzgwDQYJKoZIhvcNAQEF
BQADgYEASIzRUIPqCy7MDaNmrGcPf6+svsIXoUOWlJ1/TCG4+DYfqi2fNi/A9BxQIJNwPP2t4WFi
w9k6GX6EsZkbAMUaC4J0niVQlGLH2ydxVyWN3amcOY6MIE9lX5Xa9/eH1sYITq726jTlEBpbNU13
41YheILcIRk13iSx0x1G/11fZU8xggLnMIIC4wIBATBpMGIxCzAJBgNVBAYTAlpBMSUwIwYDVQQK
ExxUaGF3dGUgQ29uc3VsdGluZyAoUHR5KSBMdGQuMSwwKgYDVQQDEyNUaGF3dGUgUGVyc29uYWwg
RnJlZW1haWwgSXNzdWluZyBDQQIDC4q5MAkGBSsOAwIaBQCgggFTMBgGCSqGSIb3DQEJAzELBgkq
hkiG9w0BBwEwHAYJKoZIhvcNAQkFMQ8XDTA0MDEyMzAxMzAzMVowIwYJKoZIhvcNAQkEMRYEFDMO
xcWpZ4qqPSlN/Eu6VJFK9nLQMHgGCSsGAQQBgjcQBDFrMGkwYjELMAkGA1UEBhMCWkExJTAjBgNV
BAoTHFRoYXd0ZSBDb25zdWx0aW5nIChQdHkpIEx0ZC4xLDAqBgNVBAMTI1RoYXd0ZSBQZXJzb25h
bCBGcmVlbWFpbCBJc3N1aW5nIENBAgMLirkwegYLKoZIhvcNAQkQAgsxa6BpMGIxCzAJBgNVBAYT
AlpBMSUwIwYDVQQKExxUaGF3dGUgQ29uc3VsdGluZyAoUHR5KSBMdGQuMSwwKgYDVQQDEyNUaGF3
dGUgUGVyc29uYWwgRnJlZW1haWwgSXNzdWluZyBDQQIDC4q5MA0GCSqGSIb3DQEBAQUABIIBADNm
secm53dKHhrEguBEU0iHWloXjmHCY1fNCNJ4FWDjWPIS1etsqKHOG9UgPFz/PnfsVBCVaT1Py434
cRsVuAS2+nqf2vr5JC5idLLLFAtNJgJvO/6VLkUt8tjYwZcfGfjsCzrOsYl7qMJz0BHHbgYaSdrl
OJHqYEzIApRjNntTvIgI/8Q9h76d4+fxjyjSaKysl8oE+q4PdudlmT2a2oGeSQqcBK+Vx0v8Sehb
dO9TpI/cxjMQBBzt0hTmem1eGGUDDAjLLJ0zNaiQQm7pcfg7TQJ+G++hjNoxvY7cLC9RzHOaj7PB
WKEXDkbrcY+aA02TuRP30f23mb0tGwvPa/sAAAAAAAA=
--Apple-Mail-4--122533140--