FC 1: Who Learns What

When you click on the dark-blue button to sign in with Facebook (or bright red for Google) what does Facebook (or Google) learn about you? What does the app you’re signing into learn about you? Uncertainty makes people nervous about federated login.
[This is part of the Federation Conversation series.]
And the answer is... · “It depends.”
Sorry. It just isn’t simple. But the single most important thing is simple, and goes like this:
You shouldn’t have to guess! · Since the answer is kind of complicated and depends on a whole bunch of factors, it’s entirely unreasonable for either the app you’re signing into (let’s call it the “RP”, identigeek jargon for “Relying Party”) or the Identity Provider (“IDP”) to expect you to know which information flows where.
So it’s crucial that everyone involved be explicit, and do a good job of explaining what they’re collecting and what they’re using it for. As in, wherever you go, there should be an easy-to-find easy-to-understand privacy policy. If there isn’t, maybe just don’t go there.
But that’s not enough. When you click on a “Sign in with” button, it should tell you right then and there what’s going to happen.
What the IDP learns · Using most federated-identity protocols (OpenID 2, SAML, OpenID Connect, anything else OAuth 2-based), the IDP learns that the sign-in happened: That such-and-such a user logged into such-and-such an app. One of the claims of the Mozilla Persona designers is they don’t necessarily let the IDP know which apps people are signing into. I haven’t done a Persona deep-dive yet, but I’ll report back after I do.
But just because the IDP knows where and when you’ve logged in, that doesn’t mean it retains the information or makes any particular use of it. Check privacy policies!
Now, I’m pretty paranoid (and more so every day I’m in this job) but this one doesn’t worry me much, here’s why:
First, just about every app I sign up for sends me a confirmation email, so my email provider (which is usually an IDP) already knows about my accounts.
Also, given the astonishing number of tracking widgets all over the web, and the fact that certain government agencies are capturing basically all Internet traffic, it’s like this: Where your browser goes isn’t very secret. So someone tracking the (fairly rare) occasions when I actually go through the sign-in process just doesn’t loom that large.
But I’m not saying that it’s wrong to worry about this; if it bothers you, it bothers you. And I do believe that once anyone’s connected to anywhere, the traffic should be private by default.
Anyhow, the fact of sign-in is all that’s captured. The IDP doesn’t learn anything new aside from that; in fact, the information flow is all the other way, from IDP to RP. That is to say, just because you signed in somewhere with Facebook doesn’t mean Facebook gets to find out about what you do once you’re there. (Unless the app is using other Facebook APIs... did I mention that this is complicated?)
What the RP learns · It’s all over the map; when you sign in to some RP with some IDP, what the RP learns depends on what protocol you used, how much information you ask for, and what info the IDP is willing to provide. Since there’s no way for you to tell, it is critically important that you be informed what’s going on, at the time it’s going on.
Let’s explore this by example, with the Google IDP since I work there and
know it best. The absolute minimum an RP can ask for
is just confirmation that the you’re logged into the browser. (For OpenID
Connect experts, I’m talking scope=openid.) When an RP asks for
that, you see this:
Assuming you say “Yes”, Google will send the RP a success signal, plus, since you want to know who you’re talking to, a unique User ID value, which can be used to look up your “Public profile” at Google. To check out yours, go visit profiles.google.com/me, copy the URL you end up at, and visit it again in incognito mode or from another browser where you’re not signed in.
This approval page could be improved, I think. First, I know it’s obvious that you’re being logged in, that’s why you came here, but I still think it should say that yeah, it’s reporting your sign-in status. Also, the phrase “know who you are” should be linked to your public profile.
So I launched an internal conversation about this, and we’ll work on it. See, blogging improves the Internet.
What’s wrong with this picture? · That interchange was unusual, because the RP didn’t learn your email address. Sometimes you hear people saying that we’re past email, it’s 20th-century stuff, kids don’t use it. But most apps’ operators really want to know people’s emails. Among other reasons, if all other login mechanisms break down, they can always email you a “reset my password” link.
So a typical RP will also usually ask for the email (OpenID Connect experts:
scope=openid email). Then you see a screen like this:
Which I think is pretty decent. The RP can also ask for a basic
information package (scope=openid email profile) and you’ll see
this:
The “basic information” includes things like your name, your G+ profile if you have one, a picture, and your gender; but only if you’ve provided them to Google. By the way, those little i-in-a-grey-circle thingies link to longer explanations, which are pretty good.
This feels social · While that is a useful little package of information, many RPs want more. They want to enrich your experience and a really good way to do it is to get social: find out who your friends are and what you care about.
Staying in the Google context, this gets us into the territory of Google+ Sign-In, the flagship offering. It comes with loads of library support for every programming platform, useful extras like prompt-to-download-my-mobile-app, and really slick APIs.
If the RP uses it, here’s what you see:
Obviously, there’s more going on here. On the one hand, the RP can get more information; but on the other, you have very precise control. If you want, you can keep it from finding out who’s in your circles, and also from being visible in your stream.
Other than Google ·
I don’t know the numbers, but I get the impression, just looking around,
that signing in with Facebook is pretty popular. Here’s their approval screen
for scope=email.
And Microsoft’s, for scope=wl.signin wl.basic wl.emails:
Both of them are reasonably clear; but I think the Microsoft version is excellent.
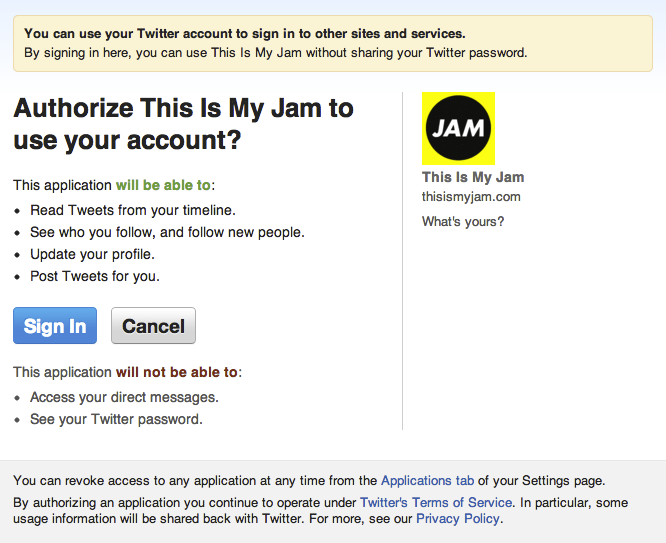
And let’s not leave Twitter out:
Looks perfectly sensible to me, and lots of apps use it. But note that Twitter does not provide an email address, which is going to limit the range of things an RP can do.
The Real Issue · It’s not technology, it’s trust. Does the person looking at the approval screen understand what it’s saying, and (most important) does he or she believe the IDP will do what he or she thinks they’re saying they’ll do?
And it’s also very situational. I’m probably totally OK with social login of some flavor for a music-sharing app, but am going to be very nervous about the slightest social whiff for medical or financial apps.
The interesting question (and we don’t have good data on this yet) is: Once we have a bigger IDP ecosystem, so there are more ways to log in, and users start seeing lots of different approval screens, what happens? I’d seriously expect the bloggers and journos to start writing positive/negative reviews of IDP performance and features.
Question: Will people punish apps that they think are asking for too much information, by walking away?
How people respond to choice is the crucial point; more important than all the technology issues put together. We have little useful data to base predictions on, so I’m not going to make any.
But I’m pretty sure that choice is good.
Comment feed for ongoing:
From: Grahame Grieve (Aug 11 2013, at 21:15)
There's a problem here, because whether I trust either the RP or the IDP depends on whether they fully inform me. An even as an OAuth implementer, I don't really know whether they've fully informed me. In fact, I expect not because there's a tension about the granularity of access offerings, between how much and how little you ask for - in order to get a particular piece of information, applications have to ask for more than they need.
So how will a normal user know that they've been informed? In the real world (say, food preparation safety) that needs standards, legislation, licensing, and inspections. Must we go there?
[link]
From: IBBoard (Aug 12 2013, at 01:04)
Looking at those examples, I think Google comes out looking the best! If I'm understanding those scopes correctly then Facebook and Microsoft are giving away contacts when all you wanted was a simple login confirmation.
Twitter permissions always annoy me, though. Often I just want a "read-only" access or "read and post but no updates/follows", but the permissions are often higher than that. Personally, I stop if the Twitter login asks for too many permissions (unless I *really* trust the app, and even then I revoke it as soon as I've finished).
"Question: Will people punish apps that they think are asking for too much information, by walking away?"
Unfortunately, I don't think it'll happen enough. The average person just doesn't think/care enough.
I've been looking at simple games on Android - nothing complex and flashy, just your "shift the blocks" type games that people have been building for decades. So many of them needed Internet permissions just to show you ads while you played, but some of them needed a huge long list of permissions (accessing contacts, keeping the phone on, overwriting the screen, etc) and yet lots of people *still* installed it!
Even worse, I saw one four- or five-star review of a game (again, a basic one that a five year old could understand and that there are dozens of alternatives to) that said "it keeps putting shortcuts and stuff to random sites on my desktop and it might have installed some extra apps, but I still love it!". When people are at that point then there is no hope for them!
[link]
From: Stuart Langridge (Aug 12 2013, at 01:54)
This was going to be a comment, but it grew. http://kryogenix.org/days/2013/08/12/federated-uncertainty talks about how the uncertainty isn't just what the RP will do with your information; everyone's uncertain about what the IDP will do with it, and that's not treated here at all.
[link]
From: Mars Eggworth (Aug 12 2013, at 02:11)
Very interesting examples! (hadn't seen any of these screens before, as have been avoiding the 'sign in with...' buttons).
Now I see the motivation:
IDPs get all the leverage that comes from 3rd parties building on top of your 'platform'
Web apps get access to as much of the user's data as they want a) without giving the user the option to decline and b) making it seem like it's a legitimate thing to ask for.
For web apps this replaces those 'give us your email login/password nag screens that I'm always seeing in linkedin (and often accidentally type my linkedin password into before I realise what it's actually asking)
As a user I think I'll run a mile!
[link]
From: Mars Eggheart (Aug 12 2013, at 02:43)
Perhaps previous comment was a little unfair, assuming this all works as designed:
<b>User</b>:
Gets: Easy login, fewer passwords to remember
Gives: Access to friends
<b>Website (RP)</b>:
Gets: Access to each user's friends
Gives: Control of login to a 3rd party
<b>IDP</b>
Gets: To be a platform
Gives: Development effort (building and maintaining the system)
I still don't think it's a good deal for the user, though.
[link]
From: Timothy Collett (Aug 12 2013, at 05:00)
But what if I don't want the RP to "make things social" for me? What if I just want to try it out, without giving it access to my entire contact list? What if I don't trust it not to immediately spam my contact list with "Why don't you try out this site? Timothy just joined!"?
I think part of the problem here is that we don't get to pick and choose which of those we grant access to. If the site we're trying to log into with our Google credentials says it wants access to our email address and contact list, we can't say, "OK, you can have my email address, because I want to log in here, but I have no need for you to see my contact list, *at least not right now*. I want to see if you're worth my time first."
[link]
From: John Roth (Aug 12 2013, at 06:15)
There are a lot of sites out there that ask you to verify that you're a real person by signing in with one of the major players: Google, Twitter, Facebook, etc.
I didn't sign in using Google for a long time because the signin screen wanted me to establish a blog! I presume that was a hack to get in the game quick, and it's fixed (sort of) now, but it poisoned the well.
I don't sign in using my Twitter account for the same reason. If the site wants to know that I've got an account somewhere (that is, I'm not totally anonamous) fine. Posting tweets under my name? No way in ----.
[link]
From: hawkse (Aug 12 2013, at 16:22)
Very good examples and explanations here. It explains perfectly why I don't want to use a federated login.
As you demonstrate, I, the user, gets *informed* about what kind of information gets shared and I can even control that information by, like you write, simply not fill out my name or upload a profile photo.
Now, what I *want* is to *choose* which information each and every RP gets. Ie, I might not have a problem sharing my real name and picture with my bank but there's no chance in hell I'll do that when I sign in to last.fm (for example).
So, either I have to let all RPs with access level 'basic information' view my mugshot or remove it completely. Not nice.
If, for each and every RP, I could limit the transaction to *JUST LOGIN*. Nothing more. Did my password match? Yep, you're in. End of story. Then, I might consider using a federated login. But again, I'd probably still want that login to be performed for that RP specific account/profile I created, linked to my IDP sign in for convenience, instead of using my real name.
Even if that was possible, there's still the problem of trusting the IDP. Not so much that they get to know which RPs I use but more of changes to terms of service, privacy policies and technical fumbles.
As for that question; 'Hell yes!'. Any other information other than simply to check that I'm logged in and I close the tab.
[link]
From: Paul Nijjar (Aug 12 2013, at 21:18)
Another reason to distrust the RP: even if it has a privacy policy that is easy to find and read, that privacy policy can change at any time with very little warning. That means I have to verify that the policy has not changed every single time I log in, if I actually care about privacy.
[link]
From: Laura Hamilton (Aug 14 2013, at 04:35)
Personally I am not a fan of social login at all, and I try to avoid it whenever possible. I'd prefer to share as little information as possible with the websites I use. (I also use Firefox and disable third party cookies, so I guess I'm more paranoid than most.)
But there's certainly a spectrum of sites I trust more (github, amazon) versus sites I don't trust at all (LinkedIn).
I do agree that providing more info on who is getting what information is a step in the right direction. But I fail to see why any app should be able to post it's own marketing messages on my account. That should be disabled by default.
[link]
From: blufive (Aug 14 2013, at 12:16)
The key thread I’m seeing here is that the decision about what information/privileges get shared with the RP is taken by the RP and IDP in collaboration. The only vote the actual user gets is a flat Yay/Nay veto over what those two decide between them.
“Question: Will people punish apps that they think are asking for too much information, by walking away?”
I think the answer here is “yes” – and the “apps” that are getting punished more than any other are IDPs and federated login systems. After the first couple of times when an IDP tries to grant a scary privilege, like “post to my twitter feed”, to some flaky RP, the user decides that they’re never going to use that IDP for federated login. After burning through a couple of IDPs, the user decides the problem is federated login itself, and goes back to passwords (or doesn’t bother logging in at all).
At risk of self-selection sample bias, I would also suggest that maybe the early adopters who drive uptake of this sort of tool/system are more likely to be the kind of people who get twitchy about privacy and tracking.
[link]
From: hawkse (Aug 17 2013, at 13:06)
So, just saw your live show on the federation topic and got some more input.
At the beginning of your show, you correctly identify the issue as one of trust. That trust is - to a large extent - based on the privacy policies of the IDP and RP. You mention privacy policies several times and seem concerned to try to do your best. Very nice.
A problem, though, is that that privacy policy is in a constant flux and may change. I am a bit unusual in that respect that I *will* mostly bother to read the privacy policy upon first signing up. Reading it through on each change though, is a complete impossibility. Some sites offer a nice summary on what has changed but most simply demand I agree to the whole, revised policy again.
This is *not* OK. I shall be held to the last privacy policy to which I agreed and if there is a change to which I do not agree, well, that shouldn't be my problem. Convince me (no, forcing me to accept it "or else" doesn't qualify) and I'll accept it, otherwise *you* should have to deal with the revisions you make.
A bit off topic, sure, but it's part of the problem. If I constantly have to make sure changes aren't introduced forcing me to divulge ever more information, I won't use the services.
[link]
From: Lloyd Hilaiel (Aug 21 2013, at 13:49)
Fantastic post Tim, thank you. (lloyd here from the identity group at mozilla)
The thing that makes me uncomfortable with an upfront request to share a mound of information is that regardless of the careful wording or addition of visual indicators or precise controls, I think you don't give the average human an opportunity to make a real choice. There's a high intellectual barrier to understanding, before you've seen the features of the website, why exactly the site needs these permissions.
The other problem occurs before the user even gets to that screen - When you say "sign in with facebook", I believe theres a visceral understanding of what that means that is going to be impossible to change with language. The brand speaks louder than the words.
Recent data I have, shared by a web gaming site using Persona, showed by 68% of users choose an email address and password over the array of identity provider buttons. Social sign in as it stands today doesn't seem to be the preference for more than half of us. (and sure, more transparent and rigorous studies are needed).
I think we build real user choice and control when we focus on asking the right questions, at the right times, in the right ways - not by optimizing our all-or-nothing up front permissioning mechanisms.
I think a first step forward is to break "signing in" and "sharing data" into two separate transactions and to optimize them for clarity and usability separately.
If you delay asking me to link to google+ until I hit the share button, I now have a clearer understanding of both what you will do with my google+ account, and the value it will give to me - and I'm more likely to say yes. Not because you told me what you would do in carefully constructed prose and pictures - but because of the context in which you asked me.
Thanks again for the series of posts!
[link]